Phishing Resource Website
You are on: What is phishing?
Phishing is a common online scam designed to trick you into disclosing your personal or financial information for the purpose of financial fraud or identity theft.
Here's how it works:
- You receive an unsolicited email appearing to be from a legitimate company. A typical phishing email will give you a phoney reason, such as a security breach or contest, to trick you into providing your personal information.
- The email will often include a reason that urges you to click on a link that takes you to a fake website.
- That fake website will look authentic by copying the brand name and logo of the real company. This phoney site will ask you for personal information such as credit card numbers, account numbers, passwords, date of birth, driver's license number, and social insurance or social security numbers.
While you may think you are giving your information to a valid company, instead you are providing it to a fraudster!
Why did I receive a phishing email?
You received a phishing email simply because your email address has ended up in the hands of a fraudster.
email addresses are easily obtained and shared on the Internet – just like phone numbers and mailing addresses. But, other than having your email address, it is unlikely the fraudster knows anything else about you – not even your name.
So, these fraudsters need to do three things to be successful.
- target companies with large numbers of customers...the more, the better!
- send thousands of phishing emails in order to reach as many of these customers as possible (many of the emails are also received by non-customers).
- write the email messages in such a way as to trick people into revealing their confidential information.
Click on the above tabs to learn how you can protect yourself against this type of scam!
You are on: Recognizing Phishing Emails tab
Recognizing Phishing Emails
Phishing emails are becoming more sophisticated and can be tricky to spot. Being able to recognize phishing emails can help prevent you from becoming a victim.
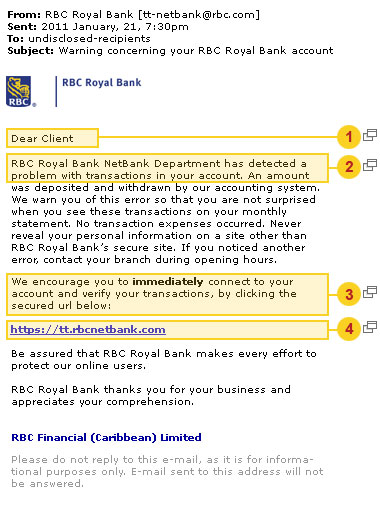
Below is an example of a phishing email. Click on the number to learn more.
Recognizing Fake Websites
A fake or "spoofed" website can look just like a company's real site. Look for these telltale signs to help you spot a fake website.
Below is an example of a spoofed website. Click on the letter to learn more.
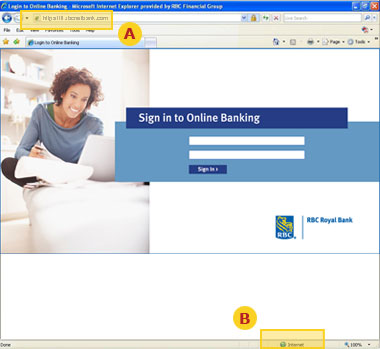
Also be wary of security alerts or unusual pop-up messages requiring input while you are on a website.
If you are unsure if the website is a valid RBC company site play it safe. Do not sign in or enter any personal information. Instead, contact us.
You are on: Protecting yourself tab
Protecting yourself
Follow these tips to help you avoid falling victim to phishing scams:
- Never provide your confidential or financial information over the Internet in response to unsolicited emails.
- Play it safe! If you don't know the source of an email or if it looks suspicious, do not open it.
- Be cautious! Even if you recognize a sender's email address, do not rely on that alone because addresses may be faked. Pay attention to the contents of the email and be careful of any embedded links.
- Never click on a link in an email that you suspect may be fake.
- Be sure! If you are unsure whether you are on a legitimate website, reopen your internet browser and type the company URL in the address bar yourself.
- Before you enter confidential or financial information online, check for the lock icon on your browser. Ensure the URL in the browser address bar starts with "https."
- Be alert! Just because an email or website appears to be from a legitimate company doesn't mean it is. Phishing schemes are designed to look real to trick users into divulging personal information for the purpose of financial fraud or identity theft.


